
Privacy-preserving computation is a hot category in crypto. Three acronyms dominate the conversation: FHE, ZK, and MPC. They're often used interchangeably. They shouldn't be. They solve genuinely different problems — and confusing them leads to projects making the wrong architectural choices.
This article gives you the honest comparison, explains where each technology excels, and explains why Aura chose FHE for what we're building.
Zero-Knowledge Proofs (ZK): Proving Without Revealing
Zero-knowledge proofs let you prove a statement is true without revealing the underlying data.
Classic example: "I know the password to this account" — proved without revealing the password. "This transaction is valid" — proved without revealing transaction details.
In crypto, ZK proofs power:
Rollups (zkSync, Starknet): Prove that thousands of off-chain transactions were computed correctly, post a single proof on-chain
Privacy coins (Zcash, Tornado Cash): Prove a valid payment without revealing sender, receiver, or amount
Identity/credentials: Prove you're over 18 without revealing your birthdate
What ZK proofs do NOT do:
ZK proofs prove correctness. They don't let you compute on private data during an ongoing operation.
If you want to build a DEX where orders stay encrypted until matching — where the matching engine itself operates on private order data — ZK proofs alone don't help. You still need to decrypt to compute the match. ZK proves the matching was done correctly, after the fact. It doesn't enable the matching to happen on encrypted data.
The ceiling: ZK hides the "who" and proves the "what." It doesn't hide the "what" during computation.
Multi-Party Computation (MPC): Distributing Secrets
MPC distributes a secret across multiple parties so that no single party can learn the secret, but together they can compute functions of it.
Example: Three banks want to compute the average of their customers' wealth without any bank revealing its customers' data to the others. MPC lets them compute the average collaboratively. Each bank only learns the final result, never the other banks' raw data.
In crypto, MPC powers:
Threshold wallets (Fireblocks, MPC-based custody): Private keys are split so no single machine holds the full key
Dark pools (some institutional trading systems): Multiple market makers jointly compute matching without revealing full order books to each other
Privacy compute networks (Arcium, others): Distributed computation where multiple nodes hold secret shares
What MPC does NOT do well:
MPC requires communication rounds between parties during every computation. The number of rounds scales with the complexity of the circuit. For simple operations like "compute the sum of two numbers," MPC is fast. For complex DeFi logic with many conditionals, multiplications, and nested operations, MPC's communication overhead becomes a bottleneck.
MPC also assumes a known, stable set of participants. If the parties are permissionless (any node can join), MPC becomes harder to secure.
And MPC's security model is trust-based: if a threshold of parties collude, they can reconstruct the secret. You're trusting that fewer than the threshold will misbehave — which is a social/economic assumption, not a mathematical guarantee.
Fully Homomorphic Encryption (FHE): Computing on Ciphertext
FHE encrypts data and lets you perform arbitrary computation on the ciphertext — without decryption at any point.
`encrypt(5) + encrypt(3) = encrypt(8)`
The addition happened on encrypted values. Nobody saw 5, 3, or 8 during the computation. The result is an encrypted 8, which only the key holder can read.
FHE enables:
A swap where the trade amount, direction, and price are encrypted from submission through execution
An order book where matching runs on encrypted orders — no party, including validators, sees the orders before settlement
A lending protocol where collateral amounts stay encrypted throughout position management
What makes FHE uniquely powerful:
Unlike MPC, FHE doesn't require multiple parties to communicate during computation. A single coprocessor can execute any computation on ciphertext. The security is based on mathematical hardness assumptions (lattice problems) — not on the honesty of participants.
Unlike ZK, FHE actually computes on private data. ZK proves that computation happened correctly. FHE lets the computation happen on encrypted inputs.
The historical problem:
FHE has been theoretically possible since 2009 but practically too slow. Every operation adds cryptographic "noise" to the ciphertext. After enough operations, noise destroys the data. The "bootstrapping" operation removes noise, but bootstrapping historically took seconds to minutes per execution.
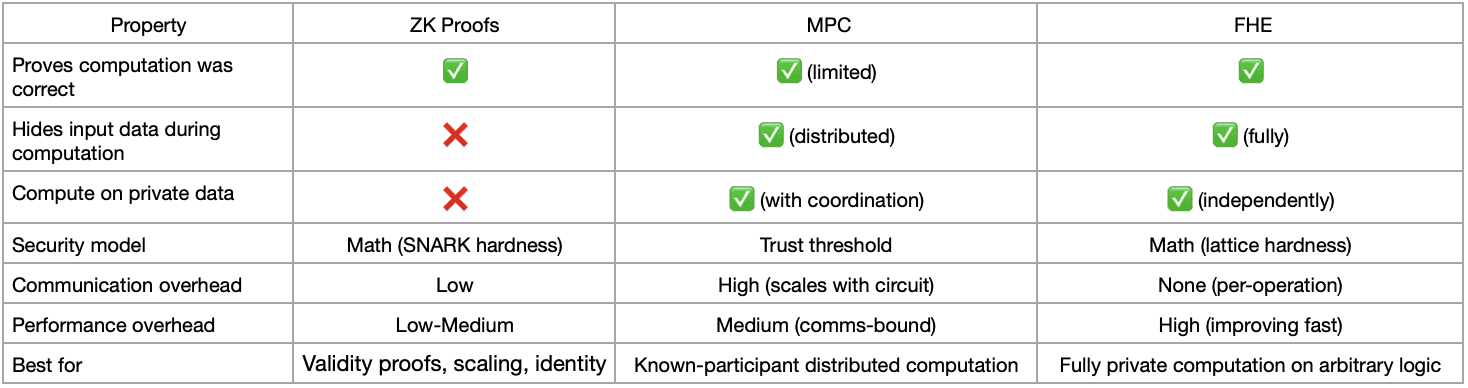
The Comparison Table
Why Aura Chose FHE
We're building encrypted swaps and a coprocessor for private DeFi on Solana. The use case requires:
Unknown participants — any user submitting a swap. MPC doesn't work well when the participant set is permissionless.
Complex computation — AMM math, slippage checks, fee calculation, order matching. MPC's per-round communication overhead would be prohibitive for circuits this complex.
Full computation privacy — the swap data must stay encrypted throughout, not just in transit. ZK alone doesn't provide this.
Mathematical guarantees — we need security that doesn't depend on validator honesty. FHE's lattice-based security doesn't break if a validator tries to cheat.
FHE was the only choice that satisfied all four requirements
Where We Are Today
Shield Swap on Solana mainnet uses FHE for encrypted execution. The SDK launching April 7 gives developers access to the same primitives: encrypt, compute homomorphically, threshold-decrypt.
ZK and MPC are valuable tools. They're not the right tools for private computation on arbitrary logic in a permissionless blockchain context.
That's the honest comparison.